Category: Cybersecurity
OWASP Top 10 for Vibe Coding: AI-Specific Security Risks and Fixes

Learn how vibe coding introduces AI-specific security risks. Explore the OWASP Top 10 applied to AI code, with concrete examples and fixes to keep your apps secure.
- Apr 26, 2026
- Collin Pace
- 5
- Permalink
Privacy-Preserving Generative AI: Homomorphic Encryption and Secure Enclaves

Explore how Homomorphic Encryption and Secure Enclaves are solving the privacy crisis in Generative AI, moving from contractual trust to mathematical certainty.
- Apr 19, 2026
- Collin Pace
- 0
- Permalink
Securing AI-Generated Code: Comparing SAST, DAST, and SCA Tools

Stop relying on slow security scans for fast AI code. Learn how to combine AI-optimized SAST, DAST, and SCA to catch vulnerabilities in AI-generated code.
- Apr 7, 2026
- Collin Pace
- 10
- Permalink
Red Teaming LLMs: A Guide to Offensive Security Testing for AI Safety
Learn how to use offensive red teaming to secure Large Language Models. Discover tools like NVIDIA garak, identify prompt injection risks, and build a safety pipeline.
- Apr 5, 2026
- Collin Pace
- 9
- Permalink
Secrets Management in Vibe-Coded Projects: Never Hardcode API Keys
Learn how to secure vibe-coded projects by avoiding hardcoded API keys. Master secrets management, environment variables, and AI guardrails to prevent data breaches.
- Mar 31, 2026
- Collin Pace
- 5
- Permalink
Security Vulnerabilities and Risk Management in AI-Generated Code

AI-generated code is now common in software development, but it introduces serious security risks like SQL injection, hardcoded secrets, and XSS. Learn how to detect and prevent these vulnerabilities with automated tools, code reviews, and policy changes.
- Feb 20, 2026
- Collin Pace
- 7
- Permalink
GDPR and CCPA Compliance in Vibe-Coded Systems: Data Mapping and Consent Flows
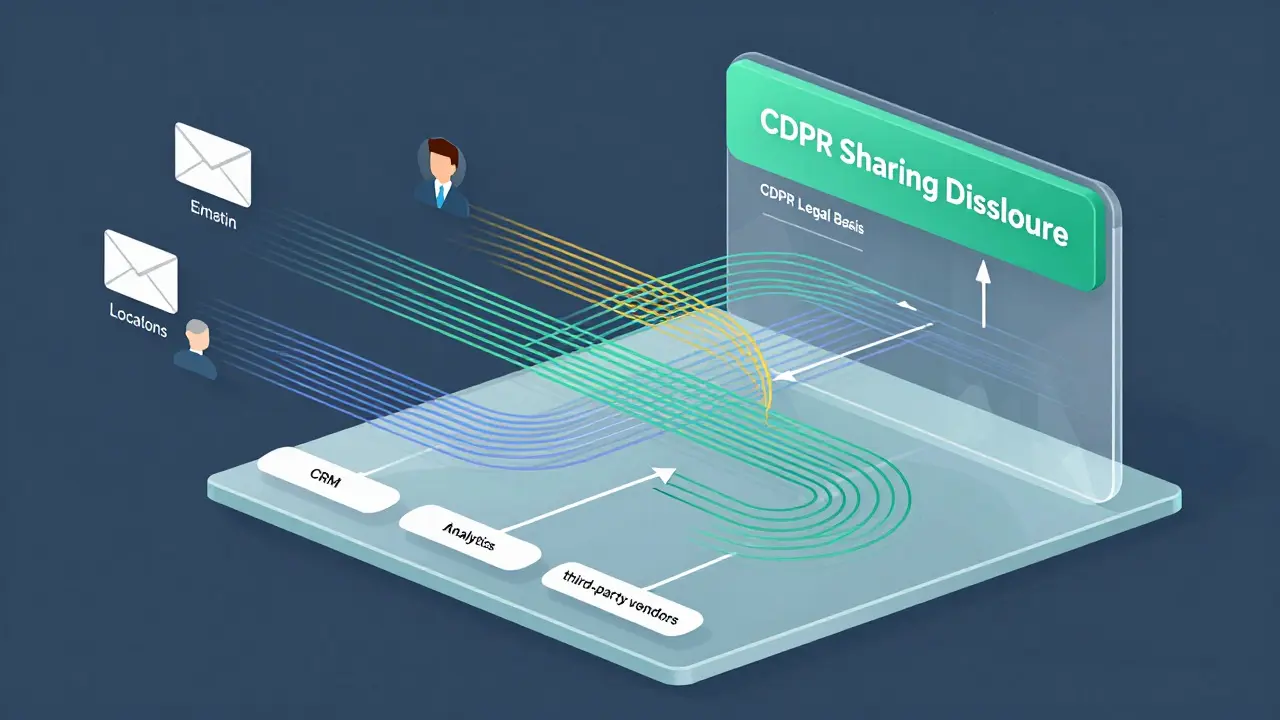
GDPR and CCPA require detailed data mapping and consent management to avoid fines and ensure compliance. Learn how to build systems that track data flows, document legal bases, and honor user rights-without relying on guesswork.
- Feb 17, 2026
- Collin Pace
- 7
- Permalink
Supply Chain Security for LLM Deployments: Securing Containers, Weights, and Dependencies

LLM supply chain security is critical but often ignored. Learn how to secure containers, model weights, and dependencies to prevent breaches before they happen.
- Jan 16, 2026
- Collin Pace
- 10
- Permalink
Input Validation for LLM Applications: How to Sanitize Natural Language Inputs to Prevent Prompt Injection Attacks

Learn how to prevent prompt injection attacks in LLM applications by implementing layered input validation and sanitization techniques. Essential security practices for chatbots, agents, and AI tools handling user input.
- Jan 2, 2026
- Collin Pace
- 9
- Permalink
How to Reduce Memory Footprint for Hosting Multiple Large Language Models

Learn how to reduce memory footprint when hosting multiple large language models using quantization, model parallelism, and hybrid techniques. Cut costs by 65% and run 3-5 models on a single GPU.
- Nov 29, 2025
- Collin Pace
- 7
- Permalink
Security KPIs for Measuring Risk in Large Language Model Programs

Learn the essential security KPIs for measuring risk in large language model programs. Track detection, response, and resilience metrics to prevent prompt injection, data leaks, and model manipulation in production AI systems.
- Aug 23, 2025
- Collin Pace
- 5
- Permalink